The recent claim that artificial intelligence (AI) has "great potential" for detecting wildfires, as suggested by a new study focused on the Amazon Rainforest, deserves closer scrutiny. The study, published in the International Journal of Remote Sensing and conducted by researchers from the Universidade Federal do Amazonas, highlights using artificial neural networks and satellite imaging technology to identify areas affected by wildfires. While the study boasts a 93% success rate in training its model, questions arise about the practical implications and limitations of relying on AI for wildfire detection.
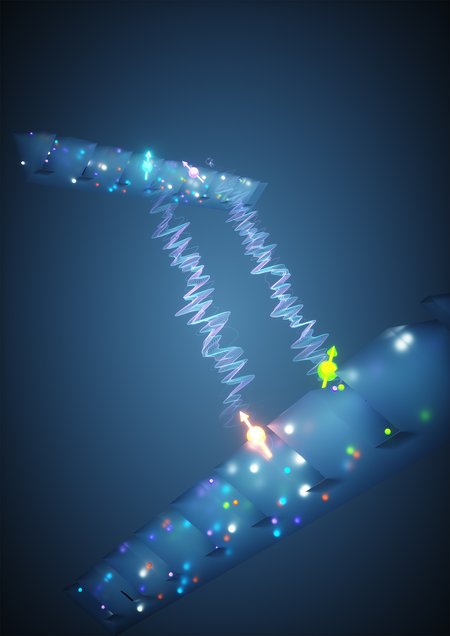
According to the research team, the Amazon Rainforest experienced a staggering 98,639 wildfires in 2023 alone, with over half originating in this ecosystem. The proposal to integrate AI technology, specifically a Convolutional Neural Network (CNN), into existing monitoring systems aims to enhance early warning systems and improve response strategies. The researchers argue that this approach could significantly improve wildfire detection and management in the region and beyond.
However, skepticism arises regarding this AI-driven solution's scalability and real-world implementation. The study's use of a relatively small dataset of 200 images to train the CNN raises concerns about the model's generalizability to diverse environmental conditions and wildfire scenarios. While achieving 93% accuracy during the training phase is commendable, the model's ability to effectively identify wildfires in practical, real-time conditions remains uncertain.
Furthermore, the authors suggest that expanding the dataset for training the CNN will enhance its robustness. While this recommendation is logical, the practical challenges of collecting and labeling a significantly larger dataset to reflect the complexity and variability of wildfires in different regions cannot be overlooked. The study's indication of potential applications for the CNN beyond wildfire detection, such as monitoring deforestation, raises questions about the technology's adaptability and reliability in addressing multifaceted environmental challenges.
The study emphasizes combining the temporal coverage of existing monitoring systems with the AI model's spatial precision. However, concerns persist regarding the reliance on AI as a standalone solution. Issues such as false positives, algorithmic biases, and the need for continuous validation and refinement based on evolving data must be addressed.
As with any emerging technology, it is critical to consider diverse perspectives to assess its viability and ethical implications. While AI shows promise in wildfire detection, carefully evaluating its operational feasibility, scalability, and long-term sustainability is essential for effective and responsible implementation.
In conclusion, although the study presents intriguing possibilities for leveraging AI in wildfire detection, a skeptical lens underscores the necessity for rigorous testing, validation, and interdisciplinary collaboration to navigate the complexities of deploying AI technology in environmental conservation and disaster management. Continued research and dialogue among experts from various fields will be crucial in determining AI's true potential and limitations in addressing the urgent challenges of wildfire detection and ecological preservation.
 How to resolve AdBlock issue?
How to resolve AdBlock issue?